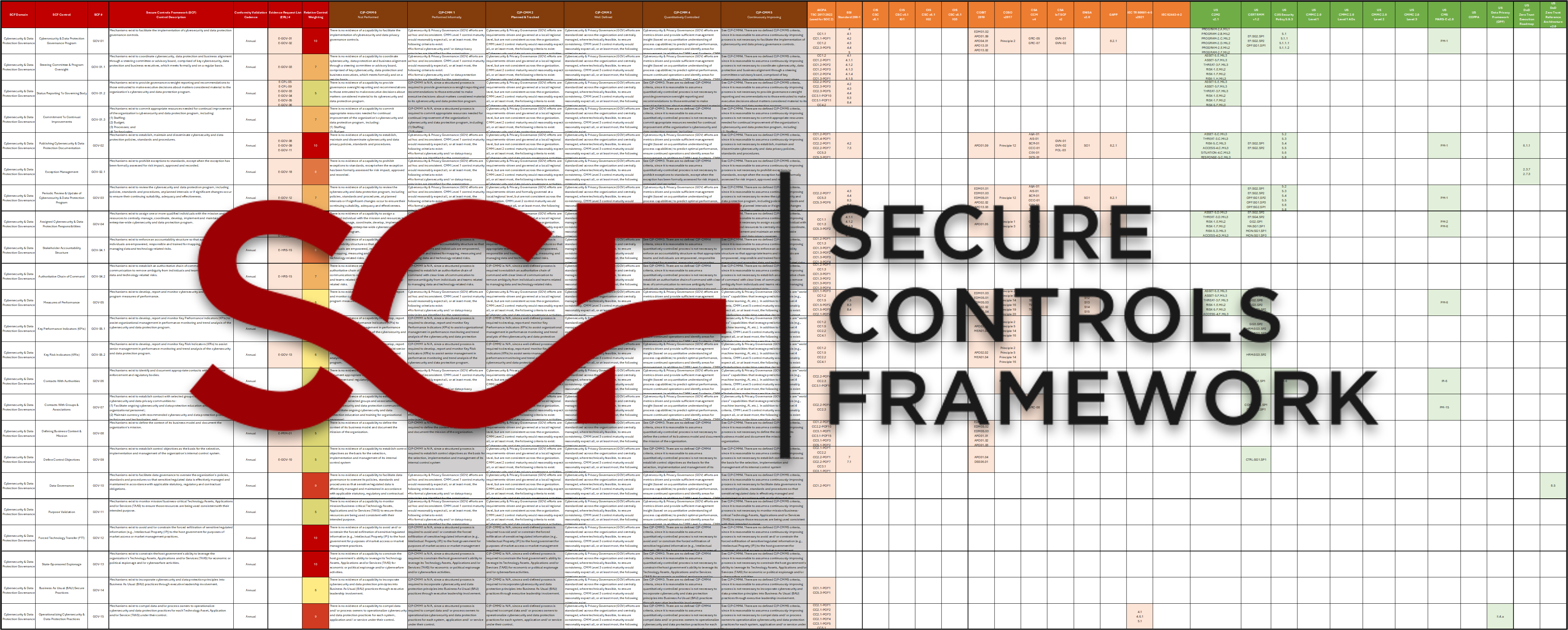
The Secure Controls Framework™ (SCF) makes compliance a natural byproduct of secure practices. It is the world's most comprehensive, free cybersecurity and data privacy metaframework — and the exclusive Common Controls Framework™ (CCF). With 1,400+ controls across 33 domains and mappings to 200+ laws, regulations, and frameworks, the SCF is the single source of truth for building a secure, compliant, and resilient organization.
The SCF focuses on internal controls — the cybersecurity and privacy-related policies, standards, procedures, technologies, and processes designed to provide reasonable assurance that business objectives will be achieved and undesired events will be prevented, detected, and corrected.
In simple terms, the SCF is a metaframework — a “framework of frameworks” — that distills 200+ cybersecurity and data privacy laws, regulations, and frameworks into a single unified control catalog. Instead of maintaining separate control sets for HIPAA, SOC 2, ISO 27001, NIST CSF, and PCI DSS, organizations use one SCF control set that satisfies all of them simultaneously.
Common Controls Framework™ (CCF): The SCF holds exclusive trademark rights to the Common Controls Framework™. The domains commoncontrolsframework.com and common-controls-framework.com both redirect to the SCF. This distinction is unique among all cybersecurity frameworks.
The SCF can be viewed as a long-term tool — not only to help with compliance-related efforts, but to ensure security and privacy principles are properly designed, implemented, and maintained.
The SCF helps implement a holistic approach to protecting the Confidentiality, Integrity, Availability, and Safety (CIAS) of your data, systems, applications, and processes. The approach looks at the following spheres of influence to identify applicable controls:
It is best to visualize the SCF as a buffet of 1,400+ cybersecurity and privacy controls. Once you know your applicable requirements, you select the controls that are right-sized for your organization — since every organization has unique needs.
The SCF sits at the center of all applicable obligations
Understanding what the SCF does and does not do is essential to using it effectively. There's no sales pitch — the SCF is free. But it's not a magic bullet either.
For organizations with 3 or more compliance requirements (e.g., NIST CSF + ISO 27001 + HIPAA + SOC 2 + PCI DSS), the SCF is an extraordinarily efficient solution — one well-worded control addresses multiple requirements simultaneously, since the same password requirement appears in dozens of laws and frameworks.
Cybersecurity is a protracted war on an asymmetric battlefield. As defenders, we have to work together — we all suffer when massive data breaches occur or when cyber attacks have physical impacts.
The SCF was created to help organizations do better with their cybersecurity practices. Hackers share attack methods freely. Why shouldn't defenders share defense methods? The SCF was built by volunteers who believe that better security practices benefit everyone.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
The SCF went live in 2018 and has grown to worldwide adoption — used by some of the largest corporations and governments globally. Its volunteers include auditors, engineers, architects, incident responders, consultants, and GRC specialists who donate their expertise because the security community wins when every organization has access to world-class controls guidance.
There is no financial incentive to push the SCF on anyone — it is completely free. The SCF Council exists purely because improving the security posture of organizations everywhere benefits society as a whole.
Where the SCF sets itself apart from every other metaframework is the depth of supporting content included — all for free.
Each control includes maturity criteria via the SCR-CMM, defining what “right” looks like at each maturity level — from basic documentation through optimized, automated controls.
Not all controls carry equal risk weight. The SCF includes proposed control weightings to help prioritize remediation and resource allocation — critical in risk management decisions.
Risks are mapped directly to SCF controls. The SCR-RMM describes how policies, standards, procedures, metrics, threats, and risks all connect through controls as the central nexus.
Threats are mapped to controls for threat-informed defense. Understanding which threats each control addresses helps right-size security investment based on your actual threat landscape.
The SCF is continuously updated as laws change, frameworks publish new versions, and emerging threats demand new controls. It evolves so your program stays current without heroic effort.
Import the entire SCF into your GRC platform via .CSV or NIST OSCAL JSON. Natively supported by dozens of enterprise GRC tools globally. No proprietary lock-in.
The SCF uses the Security, Compliance & Resilience Management System (SCRMS) — a comprehensive implementation system that treats controls as the central nexus of cybersecurity and data privacy operations. Unlike traditional GRC which is often process-centric, the SCRMS is controls-centric. In the SCRMS, controls are viewed as the nexus — or central pivoting point — for an organization’s cybersecurity program. Not just policies and standards map to controls, but procedures, metrics, threats, and risks as well. This ties everything together into a cohesive, operationalizable framework that any CISO or GRC Director can implement.
MCR defines the non-negotiable, mandatory requirements your organization must implement based on applicable laws, regulations, and contractual obligations. Failure to meet MCR creates legal exposure, regulatory sanctions, or contract breaches.
MCR is your compliance baseline: the floor below which you cannot go without accepting unacceptable risk or legal liability.
DSR defines additional security practices an organization chooses to implement based on risk appetite, business strategy, or industry best practices — beyond what is strictly mandated. These improve security posture without being legally required.
DSR is your security aspirational ceiling — the “nice to have” controls that harden your posture beyond the compliance floor.
The SCF implements the PDCA (Plan-Do-Check-Act) cycle as the foundational approach to building and operating a cybersecurity program. Each phase maps directly to the SCRMS and the SCF control structure.
Define scope, applicable laws/regs/frameworks, and risk appetite. Identify MCR and DSR. Select applicable SCF controls. Build your Minimum Security Requirements (MSR) blueprint.
Implement selected controls. Publish policies, standards, and procedures. Assign stakeholder accountability. Leverage the SCRMS as a “paint by numbers” implementation guide.
Assess control effectiveness via the SCF Conformity Assessment Program (SCF-CAP). Measure maturity using the SCR-CMM. Monitor using built-in risk and threat catalogs.
Remediate gaps from the Check phase. Update controls as laws change via the Living Control Set. Continuously improve. Prove compliance to regulators, auditors, insurers, and customers.
The SCF is built on the principle that security and privacy must be “baked in” — not bolted on. Two complementary design philosophies underpin the entire framework.
Security by Design means security is addressed at the strategic, operational, and tactical levels — built into the design of systems, processes, and products from the start rather than applied as an afterthought. The SCF’s 33-domain structure enforces SbD by providing controls at every layer of the organization — from governance (GOV) through technical controls (NET, IAC, CRY) and operations (IRO, MON, VPM). Requirements originate from statutory law, regulatory agencies, contractual obligations, and industry best practices. The SCF distills all of these into a single, consistent security design language.
Privacy by Design is the principle that privacy must be proactively embedded into the design of IT systems, business practices, and physical infrastructure — not added on, but built as a default. The SCF’s Privacy (PRI) domain contains 40+ controls aligned to GDPR, CCPA/CPRA, PIPEDA, and global privacy regulations, covering DSARs, PIAs, DPIAs, consent management, and more. The SCF treats cybersecurity and privacy as inseparable — both are necessary conditions of a mature, defensible program that can withstand external scrutiny. The SCF distills all of these into a single, consistent privacy design language.
The SCF uses the NIST IR 8477 Set Theory Relationship Mapping (STRM) methodology — a transparent, mathematically rigorous approach to crosswalking cybersecurity frameworks.
Unlike frameworks that use subjective “close enough” mapping, the STRM methodology applies set theory concepts (subset, superset, intersection, equal) to define the precise relationship between any two controls in different frameworks.
The SCF is the only major cybersecurity metaframework that participates in the NIST OLIR (Online Informative Reference) program — providing machine-readable, NIST-registered control crosswalks.
The SCF participates in the NIST OLIR program — providing machine-readable, NIST-registered crosswalks that are publicly available and independently verifiable.
Now that you understand what the SCF is, dive deeper into each component of the framework.
Learn how to implement the SCF using the Security, Compliance & Resilience Management System — the “how to use the SCF” guide for CISOs and GRC directors.
Explore all 33 SCF domains interactively. Search, filter by category, and understand the principles governing each area of cybersecurity and data privacy.
Understand NIST IR 8477 Set Theory Relationship Mapping — the transparent methodology behind the SCF’s crosswalking of 200+ frameworks.
Download the SCF now — as an Excel spreadsheet, CSV, or via GitHub. No cost, no friction, no registration required. Start building today.
Download the SCF free and start building your unified cybersecurity control set today.